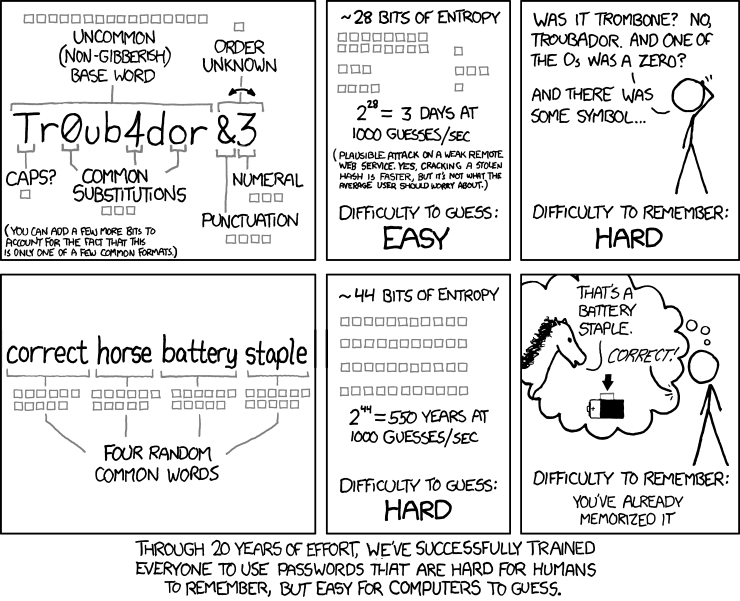
A few years back XKCD, as it so often does, got me thinking; this time about my choice of passwords. Up until that point I had always seen it as an intellectual challenge to memorize long random passwords for all my logins; usually 16 random characters, numbers, and symbols. But I've since learned that it is easier, and more importantly, more secure, to pick easy to memorize passwords. But how can we do this and still ensure the password is actually secure, it seemed a more in-depth analysis was in order.
Picking a Secure Password
The first thing we need to break down is the bits of entropy mentioned in the original XKCD comic; what is that all about? Simply put if i had a password that was a single bit long it would basically be either a 1 or a 0, therefore it has a single bit of entropy. This means there are only 2 possible passwords, and as such it would be extremely easy to guess. However when we evaluate words, instead of letters or numbers, we have to ask "how many possible words are there?". If we were truly picking from every single word in the English language this would be huge; there are tens or even hundreds of thousands of words in the English language. However in reality your vocabulary probably isn't quite so comprehensive, and even if it were it might be hard to remember a password like this one.
Pseudoturbinal_Huswifery_Climbable_Eburin
Instead we want to choose a more limited, and easier to remember, vocabulary from which to generate our passwords. Similarly if we want to calculate the difficulty in hacking a password, via a brute force attack, we should recognize the possible vocabulary we want to target. For example if I chose to write a script to hack your account, and the script tries every possible combination of the 200 most common vocabulary words in various sequences, then it will eventually hack your account; it is just a question of how long it would take.
Lets run those numbers and see what we get. How long would it take to hack your password if you picked 4 words from the 200 most common English words, assuming the script used to hack the account could make 1000 guesses per second.
\\(200^4 = 1,600,000,000\\) possible passwords
\(\frac{1,600,000,000}{1,000} = 1,600,000\) seconds
\(\frac{1,600,000}{60} = 26,667\) minutes
\(\frac{26,667}{60} = 444\) hours
\(\frac{444}{24} = 18.5\) days
For fun we can also figure out how many bits of entropy that represents.
\\(1,600,000,000 = 2^n\\)
\(n = \frac{log(1,600,000,000)}{log(2)}\)
\(n \approx 30.575\)
Of course we can't have a fraction of a bit, so we round n up to the nearest whole number indicating that the current password scheme would give us exactly 31 bits of entropy.
It is clear from the math above that there are 1,600,000,000 possible passwords that can be created when using 200 of the most common English words combined in any combination of 4 words. If we can try each possible combination at a rate of 1,000 per second then it would only take 18.5 days to determine the password. In reality this is doable on a basic desktop computer, and could be hacked in a much shorter time on a Mainframe computer. Clearly that won't do.
If we truly want a secure password we are going to have to increase the number of bits of entropy, but hopefully without making the password significantly more difficult to remember. One way we can do that, as we already discussed, is simply by increasing the vocabulary used to generate your password. Lets try it with a vocabulary of 5,000 words.
\\({5,000}^{4} \approx 6.25 \cdot {10}^{14}\\) possible passwords
\(\frac{6.25 \cdot {10}^{14}}{1,000} \approx 6.25 \cdot {10}^{11}\) seconds
\(\frac{6.25 \cdot {10}^{11}}{60} \approx 1.041 \cdot {10}^{10}\) minutes
\(\frac{1.041 \cdot {10}^{10}}{60} \approx 1.736 \cdot {10}^{8}\) hours
\(\frac{1.736 \cdot {10}^{8}}{24} \approx 7.233 \cdot {10}^{6}\) days
\(\frac{7.233 \cdot {10}^{6}}{365} \approx 19,818.61\) Years
and the entropy...
\\(6.25 \cdot {10}^{14} = 2^n\\)
\(n = \frac{log(6.25 \cdot {10}^{14})}{log(2)}\)
\(n \approx 49.151\)
Well that looks much better. Now we have 50 bits of entropy which would take about 19,818.61 years at 1,000 tries per second to figure out your password. That is probably secure enough, however a Mainframe could probably still crack it in under a year. But unless the CIA is trying to get into your account, you are most likely safe if you wanted to stop there. For reference check out this site for a list of the 5,000 most common words in the English language. You can even use this list to generate your password by picking words from the list at random.
Still I am left wondering if there are any other simple steps we can take to increase the security without sacrificing anything. One thing you can do is add one more word into the mix that is not in the list of 5,000 most common English words, but still easy to remember; even better if the word is entirely unique. Some good examples might be a friend's nick name, an uncommon last name of a friend, or a proper noun of an obscure person, place, or thing; a good example would be a character from a little known book or play. This would expand the vocabulary needed to hack the account well beyond the 5,000 word vocabulary and as such would significantly increase the Security of the chosen password.
Make It Easy to Remember
Now that we know how to pick a secure password it still may not be terribly easy for you to remember. One trick you can use to get around that is to make your passwords into sentences that are easier to remember, but obscure enough that it isnt easy for a computer to guess. The following are a few examples.
SunDestroysVirginFlowers
AppleHurtsBabyTongue
LispKillsNewDevelopersJoy
To make it even easier to remember you can pick passwords which might remind you of the topic of the website it is to be used on. For example the first password of "SunDestroysVirginFlowers" might be the perfect password to use on a website for gardening. It may also help to remember if you make the sentence structure the same for every password. Here are some examples all using the same sentence structure.
HelpCatsWantLove
AdoptABabyINeedCompany
MakeJuiceQuenchThirst
In all these cases we have a verb, followed by a noun, followed by the reason the action was taken. By following a consistent structure your brain will have more clues to remember the password and thus will make remembering it much easier. Also you will notice I capitalized the first letter of each word, one variant that is slightly more obscure is to pick some other pattern of capitalization. You could pick the last letter of every word, or even the second letter, just be consistent with all your passwords so it is easier to remember.
Make Sure It Can Be Used
The only other consideration is to make sure the password can actually be used on the desired site. Also if you tend to reuse passwords, which isn't the best of ideas, then you want to make sure the password will be accepted by most websites. Since websites have some rules to make sure a password is acceptable we should pick a password that can pass most of these rules. Usually you are covered if your password has at least one of each of the following: capital letter, lower case letter, digit, and symbol. We already covered the capitalization, so all we need to throw into the mix are some digits and punctuation. Punctuation is easy, since we are already using sentence-like structures we can just throw in some punctuation.
Help!CatsWantLove.
AdoptABaby.INeedCompany.
MakeJuice,QuenchThirst!
Digits are a little more difficult. You have two options; the first is to replace letters with a number that looks similar to the letter being replaced.
3 -> B
1 -> I
7 -> T
The other option is to use the number to represent a word that has the same sound.
2 -> to, too
4 -> for
6 -> sex
8 -> ate
The key here, again, is to be consistent so you don't get confused. So for example if you choose to replace the letter with the number it looks like, make sure you replace the same letter with the same number in all your passwords. This way you don't need to remember what pattern you used on a case by case basis. It is important to note if you use the number to represent an entire word it should not replace one of the four typed words chosen earlier but rather should be in addition to it. This ensures you don't reduce the overall entropy of your password.
In the end you should wind up with some passwords like the following:
Help!Cats8AllTheFood!
AdoptABaby.No64Me.
MakeJuice4Tolkein!
Conclusions
It should be clear now that it is trivial to create easy to remember passwords that are also secure.The only other thing I'd suggest is to keep the number of passwords you need to memorize to a minimum. Use a secure password store like LastPass to store all your passwords and instead only memorize a master password for encrypting your LastPass vault. This way you can make sure your master password is secure and you only need to remember one password. I like to have about 5 or 6 passwords I memorize for all my high security stuff like root login, LastPass, or encryption keys, and then keep the rest stored in LastPass. Any password which I rely on LastPass to store I won't need to memorize so they are psudorandom strings.
I hope that helps. Stay safe everyone.